Recently, more and more platforms have been adopting two-factor authentication (2FA) to reduce fraud, with SMS two-factor authentication being the most common form. It’s a well-known fact that fraud rates diminish when phone-based verification is required online. However, the extent to which 2FA successfully reduces fraud depends heavily on how companies providing the phone verification services guard against loopholes such as open SMS websites (disposable SMS phone numbers) that offer temporary numbers for free.
Here at RingCaptcha, we guard against popular open SMS websites that give easy access to disposable SMS numbers. We were curious what companies had their 2FA bypassed the most often, so we decided to do an investigation. We went through 10 of open SMS websites and gathered over 20,000 texts (22,598 to be exact). We compiled this data and then analyzed it. We saw which companies’ two-factor authentication was getting bypassed the most and compiled a list before grouping these companies by type.
Here are our results:
22,598 texts sent through open SMS.
60.66% had been sent within a 24 hour period.
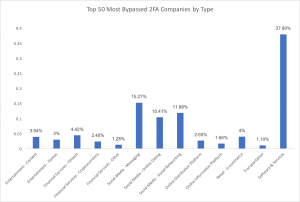
The company with the most bypassed two-factor authentication phone verification systems stood at a whopping 4.85% of all analyzed texts. Its industry is characterized as Software & Services. Unsurprisingly, this is a large company with many services that span across the globe. Although some larger companies took up larger shares of the overall amount of 2FA bypassing texts, hundreds of companies showed up in our data.
The following is a breakdown of the top 50 most bypassed companies in our data:
For Businesses:
It is important that companies understand how they or their phone verification providers prevent fraud traffic from successfully verifying. Companies who employ strategies to counter loopholes like open SMS websites are going to do a significantly better job reducing fraud on their sites.
Another good practice is to tag your texts with your company name on them. 21.73% of the texts we went through appeared to be related to user accounts & passwords but had no indication of the company’s identity that was easily traceable. Leaving a footprint allows you or your two-factor authentication phone verification provider to track whether or not your company is popping up on open SMS websites.
Another important note is the frequency of open SMS site usage. Of the 22,598 texts we analyzed, 13,708 had been sent out within a 24hr period. The biggest worry is accumulation over time. Out of the hundreds of companies with their 2FA being bypassed, many had a smaller instance count. However, after doing the math, we quickly see that the instances accrue quickly: 20 bypassed texts a day is 7,300 instances a year.
For consumers:
Don’t assume that two-factor authentication means a site is able to completely weed out fake accounts, fraud, or identity theft. It certainly can go a long way to doing so, but like any tool, how two-factor authentication is deployed is just as critical as having it in the first place.
This holds especially true for social applications, dating apps, and other forms of social media. Who you see online can still be a long way from being guaranteed to be who they say they are, even if their profile says that they have ‘verified’ their phone number.
How RingCaptcha deals with open SMS website numbers
Here at RingCaptcha, we strive to provide our customers with the best SMS/voice-based phone number verification service in the market. One way we ensure we do this, is by stopping all phone numbers on open SMS websites from verifying through our system. Each hour, we scrape these open SMS sites and add any new appearing numbers to our blacklist before applying this blacklist to all of our customers’ accounts. It is clear from our findings above that a number of SMS verification providers do not block numbers on open SMS sites, so if you are in the market for an SMS verification provider, be sure to inquire (and test!) if they block such numbers.
Further questions about our findings? Want to learn more about RingCaptcha? Drop us a line – hello@ringcaptcha.com – or write to us through our live chat on ringcaptcha.com 🙂
Below are the 10 sites we used to compile our data for this article. That said, please remember that there are many more out there and that it is important to be aware and protect against all of them:
http://www.receive-sms-online.info/
http://receivesmsonline.net/inactive_numbers.php

 Security
Security 

