 [Source]
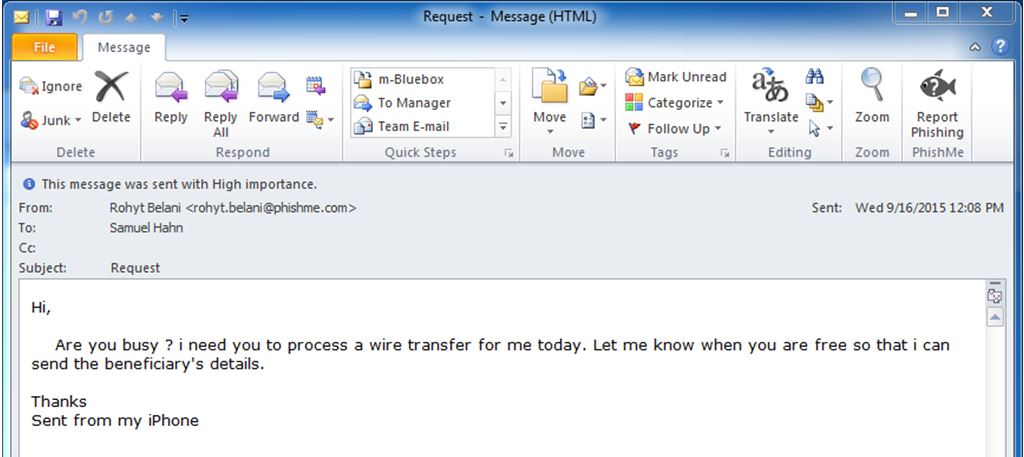
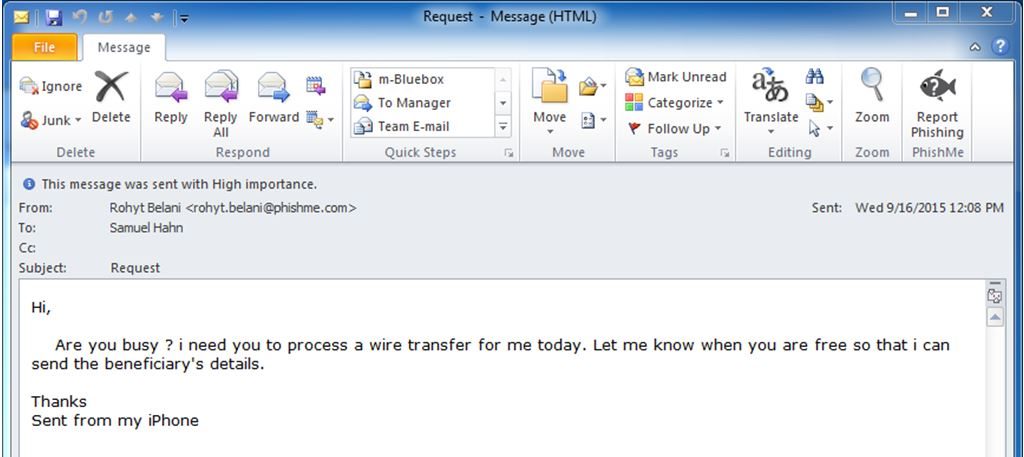
Without hesitation, you execute the transfer, safe in the knowledge you did your job well and helped the company close an important deal.
One problem: the email was a scam. Hackers had stolen your CEO's password to hijack his email and you unwittingly sent them thousands of dollars.
This is not a random occurrence. The FBI reported a 1300% rise in losses from this type of fraud, called CEO fraud or business email fraud, costing small businesses over $3 billion.
Passwords still stand at the foundation of internet and application security. They are the only padlock on billions of dollars of online data. Yet millions of passwords are stolen every day. It is estimated that over 300 billion passwords will be compromised by 2020.
Here is why our current password security practices are no longer sufficient, and some ways you can keep your accounts more secure.
[Source]
Without hesitation, you execute the transfer, safe in the knowledge you did your job well and helped the company close an important deal.
One problem: the email was a scam. Hackers had stolen your CEO's password to hijack his email and you unwittingly sent them thousands of dollars.
This is not a random occurrence. The FBI reported a 1300% rise in losses from this type of fraud, called CEO fraud or business email fraud, costing small businesses over $3 billion.
Passwords still stand at the foundation of internet and application security. They are the only padlock on billions of dollars of online data. Yet millions of passwords are stolen every day. It is estimated that over 300 billion passwords will be compromised by 2020.
Here is why our current password security practices are no longer sufficient, and some ways you can keep your accounts more secure.
Why You Need To Find a New Mom in Order to Keep Your Passwords Secure
Sometimes hackers gain more than just your email and password information. They get your mom's name. When 1,000,000,000 Yahoo accounts were hacked, the company's list of breached data weren't just the usual passwords and email addresses, but also the security questions and answers. Your secret and personal information was exposed like your mother's maiden name or the street you grew up on.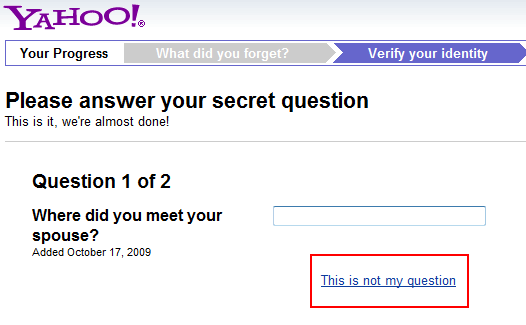 If it sounds like an invasion of privacy that can compromise all of your other accounts, you are right. Almost every online account you use adopted the same security question framework, which could enable a hacker to access other accounts even if they use different passwords.
Google security researchers analyzed the weaknesses of this approach and concluded, "Secret questions are neither secure nor reliable enough to be used as a stand-alone account recovery mechanism. They suffer from a fundamental flaw: their answers are either somewhat secure or easy to remember — but rarely both."
Google phased out security questions, requiring users to set up SMS text messages and back-up email addresses to initiate recovery of an account.
If it sounds like an invasion of privacy that can compromise all of your other accounts, you are right. Almost every online account you use adopted the same security question framework, which could enable a hacker to access other accounts even if they use different passwords.
Google security researchers analyzed the weaknesses of this approach and concluded, "Secret questions are neither secure nor reliable enough to be used as a stand-alone account recovery mechanism. They suffer from a fundamental flaw: their answers are either somewhat secure or easy to remember — but rarely both."
Google phased out security questions, requiring users to set up SMS text messages and back-up email addresses to initiate recovery of an account.
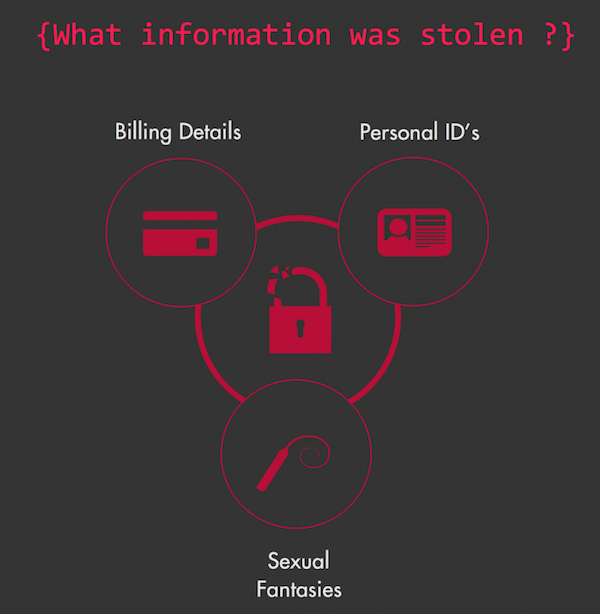
Corporate Hacks Can Get Personal And Sometimes humiliating
With more than 3,000,000,000 user credentials and passwords stolen in 2016, there is a very good chance your account information has been compromised. To check, you can use a site like haveibeenpwned.com to see whether your email and password are in any of the released data dumps.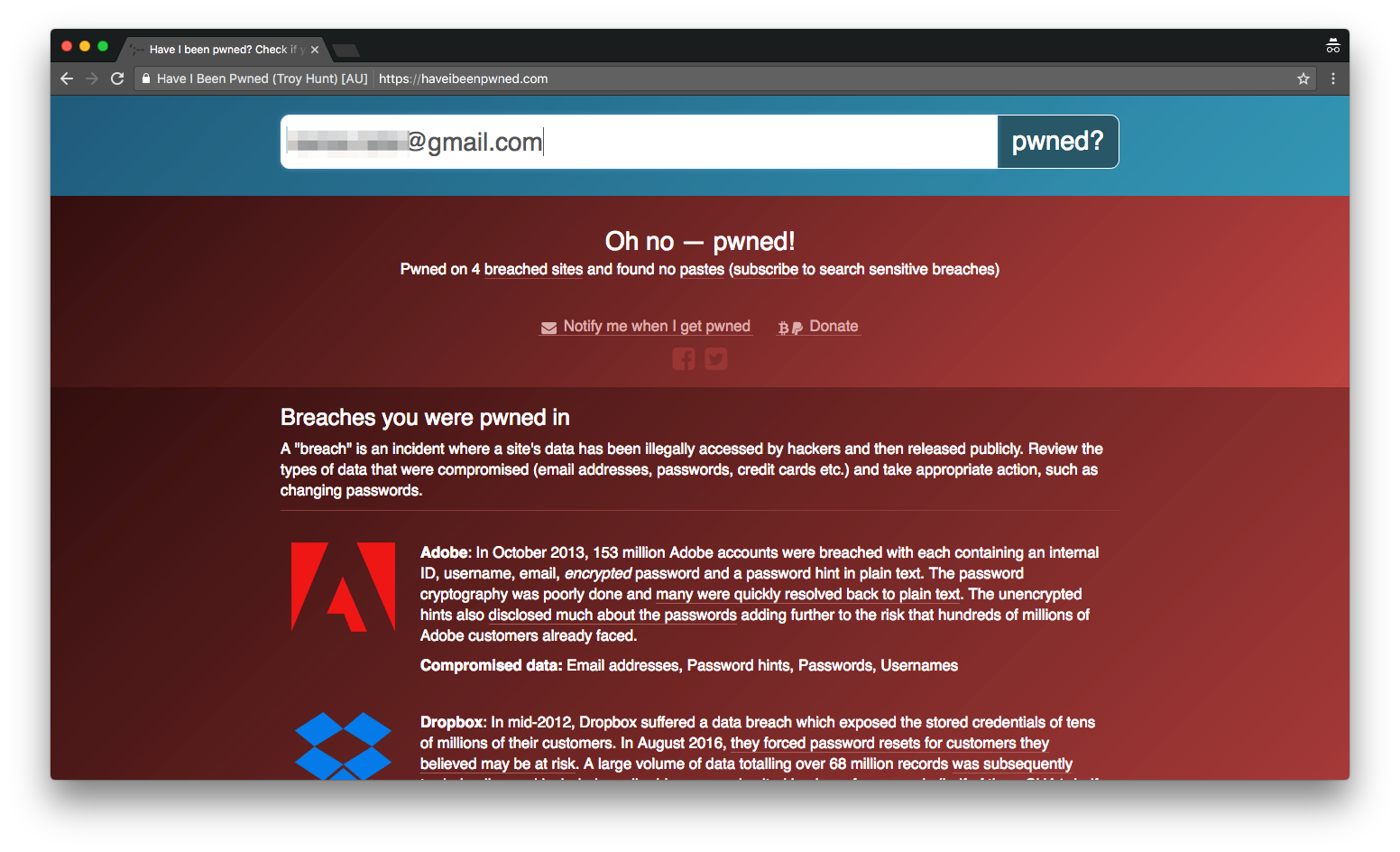 Major hacks have recently affected Twitter (32M stolen passwords), LinkedIn (167M stolen passwords), Dropbox (60M stolen passwords) and another site that has gotten plenty of press, Ashley Madison (32M stolen passwords).
Breach notifications from these companies often downplay the significance of the data stolen. They note that the hackers only gained access to email addresses and passwords, but that’s all they need to steal information that enables them to commit other crimes.
In the case of Ashley Madison - the website that connects users to engage in extramarital affairs — the very personal and perhaps humiliating secrets of 32,000,000 people were exposed. Users were then blackmailed by cyber criminals to pay $500 to remove their names from the public list.
Major hacks have recently affected Twitter (32M stolen passwords), LinkedIn (167M stolen passwords), Dropbox (60M stolen passwords) and another site that has gotten plenty of press, Ashley Madison (32M stolen passwords).
Breach notifications from these companies often downplay the significance of the data stolen. They note that the hackers only gained access to email addresses and passwords, but that’s all they need to steal information that enables them to commit other crimes.
In the case of Ashley Madison - the website that connects users to engage in extramarital affairs — the very personal and perhaps humiliating secrets of 32,000,000 people were exposed. Users were then blackmailed by cyber criminals to pay $500 to remove their names from the public list.
 [Source]
Most cyber crimes may not be as embarrassing as the Ashley Madison hack, but they can affect anyone no matter how many precautions you take.
[Source]
Most cyber crimes may not be as embarrassing as the Ashley Madison hack, but they can affect anyone no matter how many precautions you take.
Why Password Are Failing Us
Passwords have been failing us since the beginning of time. In the tale Ali Baba and the 40 Thieves, the poor woodcutter, Ali Baba, overhears the famous password, Open Sesame, and gains access to a treasure. Not much has changed today. Hackers have invented hundreds of ways to obtain your password to access their own treasures. According to Verizon’s 2017 Breach Investigations Report, 63% of all confirmed data breaches last year involved leveraging weak, stolen or default passwords. Yet, passwords remain one of the most widely used security controls to protect our personal and company data. [Source]
Here are three ways passwords continue to fail us:
1. Weak Passwords: The dilemma for most people is that good passwords are too complex to remember, but if you can remember them, they’re not effective. Because we have to remember passwords, we create easy words that hackers can quickly figure out.
Recent hacks revealed the most popular passwords included 123456, qwerty and password. But stronger passwords are also susceptible as advancements in password cracking tools enable hackers to try out 100 billion 8-character passwords per second.
2. Phishing Schemes: Personal information such as your bank account numbers and passwords are compromised by scammers who trick you into sharing your information. Phishing scams are usually delivered through emails containing a link to a fake site that mimics a trusted company to input your credentials.
Scammers have become more sophisticated, creating professional and authentic-looking emails that are hard to spot. Intel conducted a test that showed 97% of people around the world could not identify a sophisticated phishing email.
Last year's most impactful phishing scheme had nothing to do with money, but rather the Presidential Election. John Podesta, the chairman of Clinton’s campaign received an email asking him to change his password. The blunder gave hackers access to about 60,000 emails that were exposed by WikiLeaks.
3. Malware Downloads: Scammers send you emails and social media messages at random with links offering 'free' file downloads for things like music, movies or games. When you click to download, you install a secret software that can lock your files until you pay a ransom.
Malware also enables scammers to access your files and track what you are doing on your computer. They can use your passwords to steal your personal details and commit fraudulent activities with your identity.
Passwords are an antiquated security measure full of flaws and weaknesses, but for the time being we are stuck with them. That said, there are new methods and tools to help you strengthen your passwords.
[Source]
Here are three ways passwords continue to fail us:
1. Weak Passwords: The dilemma for most people is that good passwords are too complex to remember, but if you can remember them, they’re not effective. Because we have to remember passwords, we create easy words that hackers can quickly figure out.
Recent hacks revealed the most popular passwords included 123456, qwerty and password. But stronger passwords are also susceptible as advancements in password cracking tools enable hackers to try out 100 billion 8-character passwords per second.
2. Phishing Schemes: Personal information such as your bank account numbers and passwords are compromised by scammers who trick you into sharing your information. Phishing scams are usually delivered through emails containing a link to a fake site that mimics a trusted company to input your credentials.
Scammers have become more sophisticated, creating professional and authentic-looking emails that are hard to spot. Intel conducted a test that showed 97% of people around the world could not identify a sophisticated phishing email.
Last year's most impactful phishing scheme had nothing to do with money, but rather the Presidential Election. John Podesta, the chairman of Clinton’s campaign received an email asking him to change his password. The blunder gave hackers access to about 60,000 emails that were exposed by WikiLeaks.
3. Malware Downloads: Scammers send you emails and social media messages at random with links offering 'free' file downloads for things like music, movies or games. When you click to download, you install a secret software that can lock your files until you pay a ransom.
Malware also enables scammers to access your files and track what you are doing on your computer. They can use your passwords to steal your personal details and commit fraudulent activities with your identity.
Passwords are an antiquated security measure full of flaws and weaknesses, but for the time being we are stuck with them. That said, there are new methods and tools to help you strengthen your passwords.
How to Toughen Up Your Password Security
There is no one thing that will make your password secure. The best you can do is implement a number of best practices and new tools to make your passwords really hard to crack. From a business perspective, every company must implement a multi-layered security approach. Here is a three-step layering framework that includes authentication and encryption to secure your passwords: Layer 1: Create Stronger Passwords: The longer the password, the harder it is for a hacker to break. Make passwords at least eight characters long, use a mixture of letters, numbers, capitals and special characters and change every month or three. Omit duplicates by using a unique password for each of your accounts. You can use this site to test your password. Layer 2: Two-factor authentication for all accounts. Security professionals recommend using multiple authentication factors: “something you know”, like your password, and “something you have”, like an authenticator app on your phone. It is said that 80% of breaches could have been avoided had the businesses used 2FA.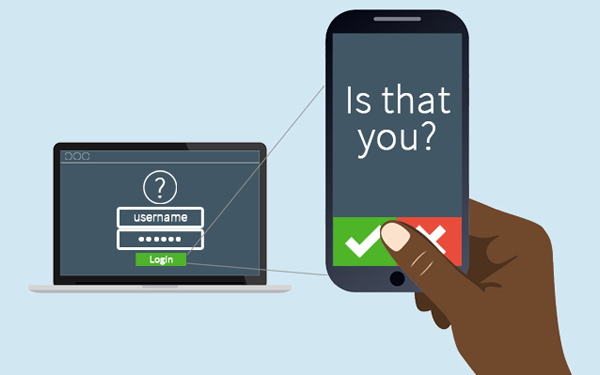 [Source]
Using a 2FA tool like RingCaptcha will create a higher barrier for potential hackers to access your accounts, even if your password is stolen through a phishing scheme or malware download.
For companies that offer online accounts or applications, using 2FA during the onboarding process is a great way to build trust and educate your customer that you are taking extra measures to secure their data.
Layer 3: Encrypt your password. Technically speaking, encryption converts electronic data such as your password into another form, called ciphertext, which cannot be easily understood by anyone except authorized parties.
You don't need to be technical to encrypt a password. Try a user-friendly password management tool like 1Password to secure and share passwords. Businesses have embraced these management tools as a secure method for keeping passwords safe from their employees' weaker password entries.
[Source]
Using a 2FA tool like RingCaptcha will create a higher barrier for potential hackers to access your accounts, even if your password is stolen through a phishing scheme or malware download.
For companies that offer online accounts or applications, using 2FA during the onboarding process is a great way to build trust and educate your customer that you are taking extra measures to secure their data.
Layer 3: Encrypt your password. Technically speaking, encryption converts electronic data such as your password into another form, called ciphertext, which cannot be easily understood by anyone except authorized parties.
You don't need to be technical to encrypt a password. Try a user-friendly password management tool like 1Password to secure and share passwords. Businesses have embraced these management tools as a secure method for keeping passwords safe from their employees' weaker password entries.

 Security
Security