Reduce your exposure to ransomware by onboarding new customers and members with SMS user verification
A digital hostage crisis has already hit half of all companies, and the problem is worsening at a record pace: Ransomware.
This type of attack seizes files or systems and demands payment for access — with threats continuing to evolve in severity and sophistication.
But just like the analog version of this type of crime, paying the ransom doesn’t necessarily make the problem go away. The ransomware can ask for more money (right away or come back later on for another attack).
Or, worse, the attacker might just take the money and run, so to speak: One in five businesses that paid the ransom never got their material back, according to a survey by Kapersky Labs.
While Kapersky has seen a nine-fold increase in ransomware over the past year, SonicWall reported a 167-fold increase, documenting 634.2 million instances in 2016.
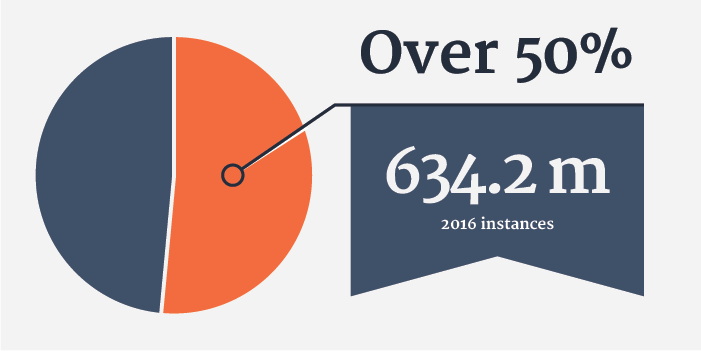
Over half of all companies have experienced ransomware attacks, amounting to 634.2 million instances in 2006, according to SonicWall.
Nine Digits and Rising
While that figure includes blocked attempts, enough of them succeeded to score $209 million from U.S. victims in just the first three months of 2016, according to the FBI, as cited by Reuters.
Fear of negative publicity was the primary motivator for the 48% of businesses that paid the ransom, according to the Ponemon Institute. Unfortunately, keeping things quiet helps keep the average consumer unaware of the risks — so that the weakest links end up being your customers and other users outside of your organization.
Most people believe they have never been hacked, says a survey by Researchscape International. But almost half of those surveyed admit they would not be able to to tell whether they have unless someone from law enforcement or a vendor contacted them.
That mindset is exactly what ransomware campaigns play into. This becomes apparent as soon as you start looking at screenshots of ransomware campaigns. The pop-up screens increasingly emulate the types of alerts put out by law enforcement agencies and vendors of software already used by the customer.
The Lowest Hanging Fruit
“Most of the attacks rely on social engineering to trick people into activating malware,” says Larry Loeb, principal of PBC Enterprises. “Ransomware typically targets the lowest hanging fruit.”
That low-hanging fruit typically begins with spam and especially phishing — 93% of the latter contains ransomware, and phishing has increased nearly eightfold over the past year, largely as a result.
Meanwhile 53% of the companies that participated in another Ponemon Institute survey said they experience an average of 50 spam attacks per month by fake users against bona fide users. Over the course of a year, fake users victimize an average of 21% of legitimate users.
More than four out of five businesses have a problem with some form of “bad actors in their user base ecosystem,” according to the Ponemon report.
And 30% say the bad actors join the website mainly to spam other users, 27% say it’s to steal confidential information and 14% do it to try to dupe people into sharing information that might be used for fraudulent purposes.
The Ponemon report says that eliminating fake users has the potential to increase the value of a site’s user base an average of 44%, according to Ponemon. But not doing anything to respond to this problem means a loss of 47% in the value of the user base, even though fake users represent an average of 10% of a company’s user database.

One in five businesses that paid the ransom never got their material back, according to a survey by Kapersky Labs.
All About Prevention
Keeping out fake users can help prevent ransomware from coming into your organization.
The FBI recommends that organizations focus on prevention, education, and business continuity planning, “as ransomware techniques and malware continue to evolve—and because it’s difficult to detect a ransomware compromise before it’s too late.”
Unfortunately education, prevention and business continuity strategies are much more practical for enterprise users than for customers and users outside of your organization — especially prospects, who tend to back out of sign-ups that involve friction.
Indeed, 43% of companies say they don’t worry about the registration of fake accounts to avoid friction in the registration process. Only 39% say they are vigilant in determining that each user account belongs to a real person.
Rising Stakes
Yet the need to authenticate real, human users is only going to skyrocket now that ransomware has just begun to tap into a potentially scary frontier: the Internet of Things (IoT). One million of these gizmos have already been attacked.
“As IoT finds widespread applicability, organizations will need to carefully evaluate and streamline methods for device identity and authentication. Currently, [identity and access management] leaders are faced with disparate vendor specific methods, which create interoperability challenges, due to the lack of established industry standards for authentication of ‘things’ in the IoT,” said David Anthony Mahdi, research director at The Gartner Group.
His advice makes a pretty good case for using phone-based authentication to verify that customers and users are real people — it’s simple and frictionless, yet effective for weeding out would-be perpetrators of fraud, spam, and phishing, which often are the starting points for ransomware.
This makes RingCaptcha’s user authentication service the best of all possible worlds. To see for yourself, click here to get started.
We think you’ll find that RingCaptcha can reduce your exposure to a wide range of security risks, including ransomware. We’d love to hear about your experiences with this, including educating employees plus existing customers and business partners. Tell us in the comments section beneath this post — or the next time you speak to our support team. And on a final note, the video below shows how to recover from a ransomware attack.


 Security
Security 

