You never know where your next threat might originate until -- well, until it's too late -- so how do you plan for all possibilities while keeping all your bases covered? Or rather, what is the security version of the saying "think globally, act locally?" Is there such a thing?
More than one information security company promises the ability to predict the future -- or at least help make those predictions -- but if any of it worked, wouldn't the number of cyberattacks be declining instead of rising?
Companies recognize that they simply can't keep up. As recently as the summer of 2016, a whopping 87% of the 1,735 executives polled by Ernst & Young said they lacked confidence in their own organizations' level of cybersecurity.
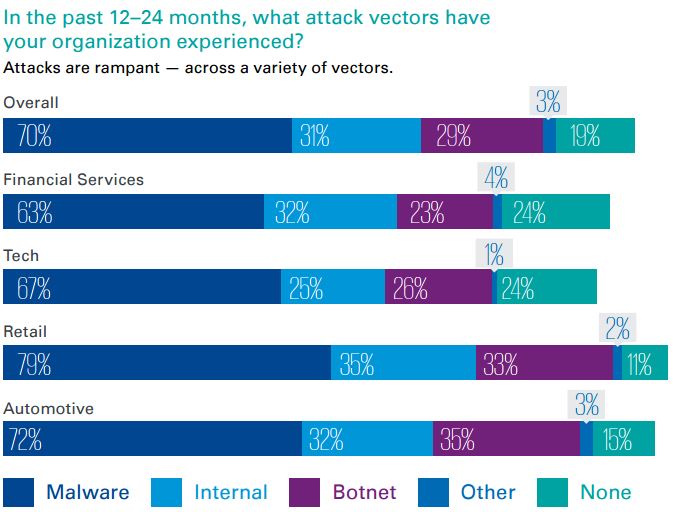
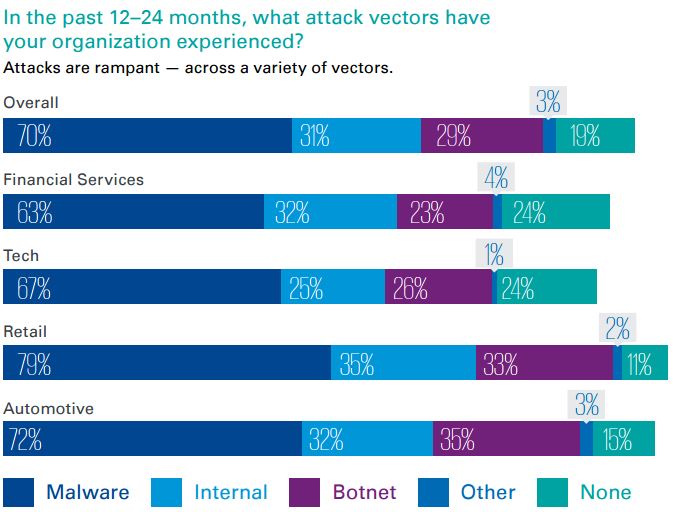
Malware appears to be the predominant type of security attack reflected in a survey by Forbes Insights and KPMG surveys of 403 corporate executives and 750 consumers.
Marketing Bubble
With these expenditures forecast to grow ever larger in response to neverending attacks with increased stakes, it's hard not to see a giant marketing bubble for technology companies that sell security solutions.
They tout ever-more complicated hardware and software, insisting that defending against hackers requires systems that need veritable rocket scientists to run them. If only there were as much supply of these wizards as the ever-growing assortment of wares they're expected to run.
The fact is, there literally aren't enough of these specialists to go around. About a third of security-related job openings remain unfilled after six months, if the right candidate for the job shows up at all.
Only one in four companies find someone with the right qualifications for the cybersecurity job; what that means in practical terms is that they have to spend time and money getting the latest security certifications training for whoever they do end up hiring.
The budget required for all that goes way beyond what any small company or startup can even contemplate. It only adds insult to injury if any technology turned out to not be used by its intended audience -- anything that overcomplicates a consumer signup or transaction tends to send them scurrying away.`
Waste Not
You can nip all of that wastage in the bud by finding a trusted service provider in security that can help you find the ideal amount of security for your situation -- something that will actually be used for what you intend.
One aspect of that could involve access, a standard best practice in security. While the specifics will vary depending on whether you are dealing with employees or customers, the general principle remains the same: Grant the least amount of access necessary to get the job done, and regularly review access privileges.
Doing this for a customer base can easily overwhelm a small business unless it can turn to a trusted service provider that can do this in a way that's user friendly for all involved is practically priceless.
You benefit from the trusted third party having access to a larger set of data on security threats, which can make trends apparent before you might be able to detect them on your own.
The third-party might already have sighted a particular phone number or email address engaging in nefarious activities on other sites and thus help you prevent any of that from coming onto your own site.
Often this type of activity happens more frequently in countries that have less mature infrastructure or weaker legislation. These are larger patterns that a trusted third party service provider will likely have more experience handling than a small business might be able to do on its own inhouse.
One of the most trustworthy providers of security as a service is RingCaptcha -- offering a powerful full-stack service that instantly enables you to onboard and verify users with a single SMS. Click here to see for yourself.

 Security
Security