Stop Bot Signups: Secure Your Funnel and Sales Team
Bot signups are becoming more frequent and more sophisticated. Stop bots muddying your funnel data and wasting salespeople’s time! Use… Continue Reading
Thanks to Our Users, RingCaptcha is in Ukrainian and Romanian Now!
Working with customers around the globe, we always come across new use cases and improve the product accordingly. Last month,… Continue Reading
Why are your Ad-spend $$$ not bringing New Paying Customers?
As the CEO of your SaaS startup, you expected a sharp uptick in revenue post launching your Google or Facebook… Continue Reading
OTP/SMS Flood Attack
(Budget Exhaustion Attack)
Protect your 2FA budget against SMS flooding attacks Overview We work with phone numbers. We send one-time PINs (OTP) through… Continue Reading
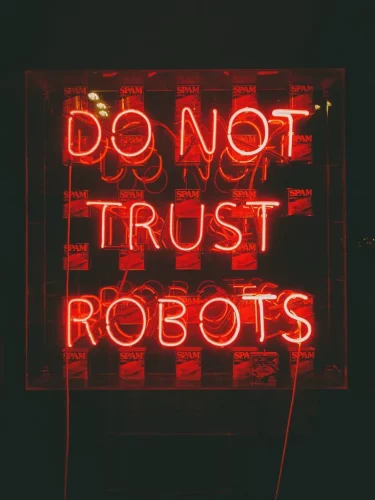
Best Practice Spam Protection
Best Practice Spam Protection- A case study DreamFactory is a SaaS API management platform that runs RingCaptcha as part of… Continue Reading
How to Reduce False Leads: A Case Study With UXPin
Most companies try to eliminate friction from their funnel. UXPin, a no-code SaaS tool, instead decided to add friction in… Continue Reading
GET STARTED NOW
Over 1 million fake leads blocked by RingCaptcha and counting!
50 SMS Free Trial • No Credit Card Required